Create and manage target groups
The following describes how to create a target group and manage target groups, including viewing the list, changing information, and configuring listener associations.
Create target group
-
Go to KakaoCloud console > Networking > Load Balancing > Target group.
-
Click the [Create target group] button at the top right.
-
On the Step 1: Configure target group screen, enter the settings, and then click the [Next] button.
Category Item Description Load balancer Availability zone Select from the availability zones available in the project Load balancer Displays the list of all load balancers in the selected availability zone Listener Displays the list of all listeners of the selected load balancer and the Do not select a listeneroptionBasic information Target group name Name of the target group Protocol Target group protocols available according to the listener protocol
- TCP listener:HTTP,TCP
- UDP listener:UDPAlgorithm - Round robin: Distributes traffic sequentially to targets in the target group
-Least connections: Distributes traffic preferentially to the target with fewer connections
-Source IP: Sends traffic from clients using the same IP header to the same targetSticky session Can be enabled or disabled only when the listener x target group combination is one of the following cases (TLS listeners are not supported)
-TCP x TCP,UDP x UDP
- Otherwise: Fixed toDisabled(inactive)Sticky session type Selectable types when the listener x target group combination is one of the following cases
-TCP x TCP: Source IP
-UDP x UDP: Source IPSticky duration Enabled only when sticky session (HTTP cookie, App cookie) is used
- Integer between 1 and 604800 (default: 3,600 seconds for HTTP cookie, 360 seconds otherwise)Cookie name Enabled only when sticky session (App cookie) is used
- The cookie name used by the user's application must be entered for App cookie
- Allowed characters: uppercase/lowercase English letters, numbers, and some special characters (!#$%^&_*+~-)
- Allowed length: 1-255 charactersHealth check Health check Set whether to use it Type Health check protocol types available according to the target group protocol
- HTTP target group:HTTP,PING
- TCP target group:PING,TCP
- UDP target group:TCP,HTTPHTTP method - Set only when HTTPis selected as the health check typeHTTP version - Set only when HTTPis selected as the health check type
- Select1or1.1HTTP status code - Set only when HTTPis selected as the health check type
- Enter a single code, multiple codes separated by commas, or a code range specified with a hyphen (-)Check path Enter in URL format Check interval Integer between 1 and 3600 (default: 30 seconds). Must be set only to a value greater than the timeout Timeout Integer between 1 and 900 (default: 5 seconds). Must be set only to a value smaller than the check interval Threshold for state change (success) Integer from 1 to 10 (default: 5 times) Threshold for state change (failure) Integer from 1 to 10 (default: 2 times) infoWhen the algorithm is set to
Source IP, traffic sent from one source is delivered only to a specific target. Therefore, no separate sticky session setting is required, so this feature is disabled. Since sticky session settings specify a retention time, usingSource IPis recommended if you want to keep the sticky session continuously. -
On the Step 2: Add targets screen, you can add resources in the same availability zone and VPC (Virtual Private Cloud) as the load balancer selected in Step 1 as targets.
-
Select the instance to add as a target and enter the port number.
-
Click the [Add target] button.
cautionFor DSRNLB, the protocol of the connected listener and the target port number of the target group must be the same, and a target group already connected to another listener cannot be connected to a different listener. In addition, all target instances in one target group must be configured with the same port number.
-
After adding targets, click the [Next] button.
-
On the Step 3: Advanced settings screen, you can modify the detailed settings below. After modifying the values or leaving the default values unchanged, click the [Next] button.
-
On the Step 4: Review screen, review the configured information and click the [Create] button.
After creating a target group, you must configure the security group settings of the targets.
In Target group details > Targets tab, check the health check IP addresses and add those IP addresses to the inbound rules of the target's security group.
Manage target groups
On the target group details page, you can modify or delete existing target groups or add new targets.
View target group list and basic information
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Check the target group list and basic information.
Category Description Name Displays the target group name entered when created ID Displays the ID assigned when created Provisioning status Indicates whether the target group was created successfully or whether modification or deletion is in progress Operating status Indicates whether the created target group is available for use Protocol Protocol used to route traffic to the target Load balancer Displays the name of the load balancer connected to the target group Load balancer ID Displays the ID of the load balancer connected to the target group VPC Displays the name of the VPC that includes the load balancer Created at Displays the date when the target group was created [⋮] button Provides the following functions
- Rename, Configure listener association, Set algorithm, Configure targets, Set traffic weight, Configure health check, Set health check port, Configure sticky session, Delete
View target group details
-
Go to KakaoCloud console > Networking > Load Balancing > Target group.
-
Select the target group whose details you want to view.
-
Check detailed information in each tab of the details page.
- Details tab
- Connected load balancer tab
- Listener tab
- Health check tab
- Targets tab
- Monitoring tab
Item Description Name User-defined name used to identify the target group ID Unique identifier automatically assigned when the target group is created Provisioning status Progress status of resource creation/change operations Operating status Current operating status of the target group Protocol Communication protocol used by the target group (for example, HTTP, HTTPS, TCP) Algorithm Method of distributing traffic (for example, round robin) Created at Date and time when the target group was created Item Description Name Name of the load balancer connected to the target group ID Unique identifier of the load balancer Type Type of load balancer (for example, Application, Network) Provisioning status Progress status of load balancer resource creation/change Network information Information about the connected VPC, subnet, and availability zone Item Description Protocol:Port Communication protocol and port number of the listener ID Unique identifier of the listener Provisioning status Listener configuration application status Connection status Current activation status of the listener Item Description Health check protocol Method used to determine whether a target is healthy (for example, PING, HTTP) Health check interval Interval at which health checks are performed Timeout Maximum time to wait for a response Healthy threshold Number of consecutive successes required to determine a target is healthy Unhealthy threshold Number of consecutive failures required to determine a target is unhealthy Health check IP IP information to which health check requests are sent Item Description Healthy Number of healthy targets Warning Number of targets in warning state Error Number of targets in error state Inactive Number of inactive targets IP IP address of the registered target Port Target service port Weight Weight applied when distributing traffic Status Current health status of each target Item Description Query period Select the query range such as 1 hour, 3 hours, 12 hours, 1 day, or 7 days Auto refresh Whether data is automatically refreshed at regular intervals Metrics Monitoring metrics related to target groups such as traffic, number of connections, and error rate Graph Visually displays metrics for the selected period
Rename
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- From the [⋮] button of the target group, select Rename.
- Change the name in the pop-up window, and then click the [Change] button.
Delete target group
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- From the [⋮] button of the target group, select Delete.
- Enter the delete confirmation text in the pop-up window, and then click the [Delete] button.
Configure listener association
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- From the [⋮] button of the target group, select Configure listener association.
- Change the listener association settings in the pop-up window, and then click the [Apply] button.
A DSRNLB target group can be connected to only one listener created on a single DSRNLB.
Set algorithm
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Select [⋮] > Set algorithm for the target group.
- Change the algorithm in the pop-up window, and then click the [Apply] button.
Configure targets
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Click the target group for which you want to change target settings.
- On the details page, click the Targets tab, and then click the [Configure targets] button.
- In the pop-up window, check the registered targets, delete or add targets, and then click the [Apply] button.
- To revert to the initial state while modifying targets, click the [Revert] button at the top of the added target list.
caution- All targets configured in one target group must use the same port number.
- When using DSRNLB, the load balancer and the target instances must be in the same subnet.
Set traffic weight
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Select the target group for which you want to change traffic weight settings.
- On the details page, click the Targets tab, and then click the [Set traffic weight] button.
- Change the weight in the pop-up window, and then click the [Save] button.
Item Description Weight Traffic distribution value set for the target. The greater the value, the more traffic is delivered
- Enter as an integer between0and256Weight conversion (weight/256)*100 (rounded up to the first decimal place) Ratio Weight conversion / total sum of weight conversions IP Private IP address of the target to which traffic is delivered Instance Displays the name of the connected instance Instance ID Unique ID of the connected instance
Configure health check
For DSRNLB, configure target instances is required to perform health checks correctly.
-
Go to KakaoCloud console > Networking > Load Balancing > Target group.
-
Select the target group for which you want to change health check settings.
-
On the details page, click the Health check tab, and then click the [Configure health check] button.
-
In the pop-up window, change whether to use health checks or modify the setting values.
Category Description Target group Name of the current target group Protocol Types available according to the protocol of the target group
- HTTP target group:HTTP,PING
- TCP target group:PING,TCP
- UDP target group:TCP,HTTPWhether to use health check Health check protocol: Health check type
-PING: Sends packets to the target and checks the response returned by the target (ICMP Ping)
-HTTP: Sends packets to the configured path and checks the response
-HTTPS: Checks responses in the same way as HTTP for targets using certificates
-TCP: Checks the status of the target using a TCP protocol portCheck interval: Target health check interval (unit: seconds)
- 1-3600 secondsTimeout: Sets the maximum time to wait for a target with delayed response (unit: seconds)
- If the specified time is exceeded, communication with the target is considered failed
- Must be set to a value smaller than the check interval
- 1-900 secondsThreshold for state change (success): If health checks succeed consecutively for the entered number of times, the target is determined to be healthy Threshold for state change (failure): If health checks fail consecutively for the entered number of times, the target is determined to be unhealthy and excluded from traffic distribution -
If the health check type is
HTTPorHTTPS, you can configure additional attributes.Category Description HTTP method Set the HTTP request method to use for health checks HTTP version Set the HTTP protocol version to use for health check requests HTTP status code Set the status code expected to be returned by the target to the load balancer
- If the target returns the HTTP status code configured by the user, the health check is considered successful
- Example of a single status code:200,201
- Example of multiple status codes:201,202,401,402
- Example of a range: 200-500Check path Enter the path for health checks based on the URL path -
Click the [Save] button.
If the target in the target group uses the SELinux option provided by the latest CentOS distribution, SELinux denies shell_exec_t calls. Therefore, PING type health checks do not work.
Configure sticky session
Sticky sessions can be configured only for some target groups depending on the listener and target group protocol.
Sticky session options by listener and target group protocol
| Target group\Listener | HTTP | HTTPS | TCP | UDP |
|---|---|---|---|---|
| HTTP | HTTP cookie, App cookie | X | X | X |
| HTTPS | X | X | X | X |
| TCP | X | X | Source IP | X |
| UDP | X | X | X | Source IP |
| PROXY | X | X | X | X |
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Click the target group for which you want to change sticky session settings.
- On the details page, click the Attributes tab, and then click the [Configure sticky session] button.
- Change whether to use it or modify the settings in the pop-up window, and then click the [Apply] button.
Configure target instances
To use DSRNLB correctly, you must apply additional configuration to the target instances configured in the target group according to the operating system. Create the instance to be designated as a target in advance, and then proceed with the tasks below. If you do not perform this task, health checks will not work properly.
Modify allowed packet forwarding IPs
- Go to KakaoCloud console > Virtual Machine > Instances.
- From the [⋮] button of the instance to configure as a target, select Modify allowed packet forwarding IPs.
- In the pop-up window, select the network interface that exists in the same VPC and availability zone as the DSRNLB among the target instance's network interfaces, enter the private IP address of the DSRNLB as an allowed packet forwarding IP, and then click the [Apply] button.
- To use DSRNLB, you must allow inbound traffic for the private IP address of the DSRNLB and the listener port number in the security group of the target instance.
Configure network settings on target instance
Additional settings according to the operating system of the target instance are required to use DSRNLB. These include Address Resolution Protocol (ARP) related settings and loopback address related settings.
- Linux operating system family
- Windows operating system family
-
Connect to the target instance through SSH.
-
Enter the commands below.
<private_ip_of_dsrnlb>is the private IP address of the DSRNLB connected to the target group to which this target instance will be configured (for example, 10.0.3.49).cautionThe commands below must be executed with root privilege. Switch first with the
sudo -icommand and then enter them.Configure network settingssysctl -w net.ipv4.conf.all.arp_ignore=1
sysctl -w net.ipv4.conf.all.arp_announce=2
ip a add <private_ip_of_dsrnlb>/32 dev lo
ip link set dev lo upKeep settings after rebootFor the settings above, you must configure them again every time the instance reboots. Additional work is required to keep the settings after rebooting the instance. For more information, see Set up crontab to automatically run scripts at boot.
-
If the target instance was created with an Ubuntu image, DNS Resolver configuration is required for proper DNS queries.
infoIf the instance uses a VPC created before February 21, 2024, add
VPC network IPv4 CIDR + 2 addressto the/etc/resolv.conffile. If it uses a VPC created after that date, add169.254.169.253.Modify /etc/resolv.confnameserver 169.254.169.253 # Add 169.254.169.253 or add "VPC network IPv4 CIDR + 2 address"
nameserver 127.0.0.53
options edns0 trust-ad
search kr-central-2.c.kakaoi.io
Reference: Keep configured DNS Resolver after reboot
-
Change the configuration of the systemd-resolved service.
sudo vi /etc/systemd/resolved.conf/etc/systemd/resolved.conf[Resolve]
DNS=169.254.169.253 (for an instance in a VPC created before February 21, 2024, VPC network IPv4 CIDR + 2) -
Restart the systemd-resolved service.
sudo systemctl restart systemd-resolved -
Link /etc/resolv.conf to systemd-resolved.
sudo ln -sf /run/systemd/resolve/resolv.conf /etc/resolv.conf
-
Set up crontab to automatically run scripts at boot
For the Linux operating system, the settings configured above are reset when the instance reboots, so they must be configured again. To ensure the settings remain applied after rebooting, you can save the configuration work above as a script file and configure that script file to run on reboot with the crontab command.
-
Open the crontab file with the following command.
Open crontab filecrontab -e -
Add code that runs automatically at reboot using the
@rebootexpression in that file.Add code to run automatically at reboot@reboot sh /<file_directory>/<file_name>Parameter Description <file_directory>Path where the file to execute is located <file_name>File name of the shell script file to run at reboot
- Example: @reboot sh /home/setup_dsr.sh -
Create the shell script to run. This example is a shell script that executes the tasks in Configure network settings on target instance and Bind process running on target instance to DSRNLB private IP.
setup_dsr.sh#!/bin/sh
sysctl -w net.ipv4.conf.all.arp_ignore=1
sysctl -w net.ipv4.conf.all.arp_announce=2
# Private IP address of the DSRNLB connected to the target group to which this target instance will be configured
ip a add 172.30.4.237/32 dev lo
ip link set dev lo up
# Bind the process running on the target instance to the private IP of the DSRNLB when using a UDP listener (run UDP server)
python3 /home/sample_python_udp_server.py -
Adjust permissions so that this script file and the Python script file can be executed. Enter the path of each file or move to the directory where the files are located before running.
Grant execute permissionchmod +x setup_dsr.sh
chmod +x sample_python_udp_server.py -
After rebooting, check whether the settings are maintained.
Check each configured item# Check ARP settings
sysctl -a | grep net.ipv4.conf.all.arp_ignore
sysctl -a | grep net.ipv4.conf.all.arp_announce
# Check loopback IP address
ip a
# Check whether the UDP Server is running properly (check the port number specified in the Python script)
netstat -tuln | grep 12345
Step 1. Install Microsoft KM-TEST loopback adapter
- In the Search box at the bottom left of the Windows desktop, search for Run and select it.
- In the Run window, enter
hdwwizand click the [OK] button. - The Add Hardware Wizard appears, and click the [Next] button.
- Select Install the hardware that I manually select from a list (Advanced).
- Select Network adapters, and then click the [Next] button.
- In Manufacturer, select
Microsoft, and in Model, selectMicrosoft KM-TEST Loopback Adapter. Click the [Next] button. - Click the [Next] button to proceed with the installation.
- After the installation is complete, click the [Finish] button.
Step 2. Configure IP on adapter
- In the Search box at the bottom left of the Windows desktop, search for Network status and select it.
- In the Network status window, click Change adapter options.
- In the Network Connections window, you can check the Ethernet displayed as Unidentified network. Right-click this Ethernet, and then select [Properties].
- In the Ethernet Properties window, select Internet Protocol Version 4 (TCP/IPv4), and then click the [Properties] button.
- In the Internet Protocol Version 4 (TCP/IPv4) Properties window, select the [General] tab, and then select Use the following IP address:. Enter the information below.
- IP address: Private IP address of the DSRNLB
- Subnet mask: 255.255.255.255
Step 3. Ignore ARP requests and configure Weak Host Model
- In the Search box at the bottom left of the Windows desktop, search for Command Prompt and select it.
- Enter the following command to configure the system not to respond to ARP requests.
<loopback_adapter_name>means the name of the adapter newly added in Step 1. Install Microsoft KM-TEST loopback adapter (for example, Ethernet).Ignore ARP requestsnetsh interface ipv4 set interface <loopback_adapter_name> metric=254 - Enter the following commands to configure the Weak Host Model.
<default_network_adapter_name>means the name of the default adapter, not the newly added adapter (for example, tap6d769000e-0a).Configure Weak Host Modelnetsh interface ipv4 set interface <default_network_adapter_name> weakhostreceive=enabled
netsh interface ipv4 set interface <loopback_adapter_name> weakhostreceive=enabled
netsh interface ipv4 set interface <loopback_adapter_name> weakhostsend=enabled
Additional configuration for target instance when using UDP listener
When using a UDP listener of DSRNLB, only the Linux operating system family is supported for the target instance. In addition, you must apply one of the following three additional configurations to use it, and even if the configuration is completed successfully, intermittent failures may occur because packet loss can happen due to the nature of UDP communication.
- Bind process running on target instance to DSRNLB private IP
- Use iptables provided by the Linux kernel for stateful NAT configuration
- Use nftables provided by the Linux kernel for stateless NAT configuration
Bind process running on target instance to DSRNLB private IP
-
Create the following example code on the target instance. This example is written in Python, but you can replace it with another programming language as needed.
sample_python_udp_server.pyimport socket
localIP = "172.30.4.237" # Private IP of the DSRNLB
localPort = 12345 # Port number used by the UDP Server run and created by this source code
bufferSize = 1024
msgFromServer = "Hello UDP Client, this is Simple UDP Server."
bytesToSend = str.encode(msgFromServer)
# Create a datagram socket
UDPServerSocket = socket.socket(family=socket.AF_INET, type=socket.SOCK_DGRAM)
# Bind to address and ip
UDPServerSocket.bind((localIP, localPort))
print("UDP server up and listening")
# Listen for incoming datagrams
while(True):
bytesAddressPair = UDPServerSocket.recvfrom(bufferSize)
message = bytesAddressPair[0]
address = bytesAddressPair[1]
clientMsg = "Message from Client:{}".format(message)
clientIP = "Client IP Address:{}".format(address)
print(clientMsg)
print(clientIP)
# Sending a reply to client
UDPServerSocket.sendto(bytesToSend, address) -
Run the example code.
Use iptables provided by the Linux kernel for stateful NAT configuration
Additional CPU is used for NAT processing, and because DNAT is stateful, memory consumption can also be high.
-
Create the following example code on the target instance. This example is written in Python, but you can replace it with another programming language as needed.
- This example code is the same as above, but the
localIPaddress is changed to0.0.0.0.
sample_python_udp_server.pyimport socket
localIP = "0.0.0.0"
localPort = 12345 # Port number used by the UDP Server run and created by this source code
bufferSize = 1024
msgFromServer = "Hello UDP Client, this is Simple UDP Server."
bytesToSend = str.encode(msgFromServer)
# Create a datagram socket
UDPServerSocket = socket.socket(family=socket.AF_INET, type=socket.SOCK_DGRAM)
# Bind to address and ip
UDPServerSocket.bind((localIP, localPort))
print("UDP server up and listening")
# Listen for incoming datagrams
while(True):
bytesAddressPair = UDPServerSocket.recvfrom(bufferSize)
message = bytesAddressPair[0]
address = bytesAddressPair[1]
clientMsg = "Message from Client:{}".format(message)
clientIP = "Client IP Address:{}".format(address)
print(clientMsg)
print(clientIP)
# Sending a reply to client
UDPServerSocket.sendto(bytesToSend, address) - This example code is the same as above, but the
-
Run the example code.
-
Enter the following commands to add iptables DNAT rules.
Add DNAT rulesiptables -p udp -t nat -A POSTROUTING -j RETURN -d <private_ip_of_target> --dport <udp_server_port>
iptables -p udp -t nat -A PREROUTING -j DNAT --dport <udp_server_port> --to-destination <private_ip_of_target> -d <private_ip_of_dsrnlb>Item Description <private_ip_of_target>Private IP address of the target instance itself <udp_server_port>Port number configured in the example code above (localPort value) <private_ip_of_dsrnlb>Private IP address of the DSRNLB connected to the target group to which the target instance will be configured
Use nftables provided by the Linux kernel for stateless NAT configuration
To use nftables, the Linux kernel version must be 4.10 or later.
-
On the target instance, create the example code in step 1 of Use iptables provided by the Linux kernel for stateful NAT configuration.
-
Run the example code.
-
Enter the following commands.
Modify source address in IP header of outgoing packetsnft add table raw
nft add chain raw postrouting {type filter hook postrouting priority 300 \; }
nft add rule raw postrouting ip saddr <private_ip_of_target> udp sport <udp_server_port> ip saddr set <private_ip_of_dsrnlb>Category Description <private_ip_of_target>Private IP address of the target instance itself <udp_server_port>Port number configured in the example code above (localPort value) <private_ip_of_dsrnlb>Private IP address of the DSRNLB connected to the target group to which the target instance will be configured
Manage targets
You can view, modify, and delete targets added to the target group.
Two health check IPs are created for each subnet that contains targets. To perform health checks, communication through those IPs must be allowed.
Refer to the View health check IP and Allow communication with health check IP sections and add inbound rules to the security group.
View health check IP
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Select the target group for which you want to view the health check IP.
- On the details page, select the Targets tab.
- Click Health check IP by subnet at the top of the tab details page to view the list of health check IPs.
Allow communication with health check IP
There are two ways to configure security groups to allow communication from health check IPs.
Choose one of the following two methods according to your preference.
First, add inbound rules that allow the IPs in the existing security group of the target instance
-
Go to KakaoCloud console > Networking > Load Balancing > Target group.
-
Select the target group for which you want to view the health check IP and allow communication.
-
On the details page, select the Targets tab.
-
Click Health check IP by subnet at the top of the tab details page to check the list of health check IPs. Keep the health check IP view open or copy the list.
-
In the Target list at the bottom of the tab details page, identify the instance for which communication from the health check IPs should be allowed, and click the security group name of that instance.
- If multiple security groups are connected, select any one of them and register it.
- If the same rule has already been added to one or more connected security groups, communication is already allowed.
-
In the Inbound rules tab of the Security group details page, click the [Add inbound rule] button.
-
In the pop-up window, click the [Add] button at the bottom of the inbound rules tab to add a new rule input field.
 Manage security group rules
Manage security group rules -
Based on the detailed information in Step 5 of the Target group > Targets tab, enter the rule information and click the [Apply] button on the right.
Category Description Protocol Protocol for communication (TCP, UDP, ICMP, ALL), selected according to the health check type of the target group
- If the health check type is PING:ICMP
- If the health check type is HTTP, HTTPS, TCP:TCPSource Source IP to allow access
- Enter the health check IP confirmed in target details
- Register each of the two health check IPs created in the subnet that contains the targetPort Port for communication
- Enter the health check port of the targetRule description (optional) Description of the rule -
Click the [Close] button at the bottom of the pop-up window to complete rule registration.
Second, create a new security group for health checks and connect it to the target instance
-
Go to KakaoCloud console > Networking > Load Balancing > Target group.
-
Select the target group for which you want to view the health check IP and allow communication.
-
On the details page, select the Targets tab.
-
Click Health check IP by subnet at the top of the tab details page to check the list of health check IPs.
Keep the health check IP view open or copy the list. -
Refer to Create security group and go to the screen for creating a new security group.
-
In the pop-up window, enter the security group name and description, and then add inbound rules.
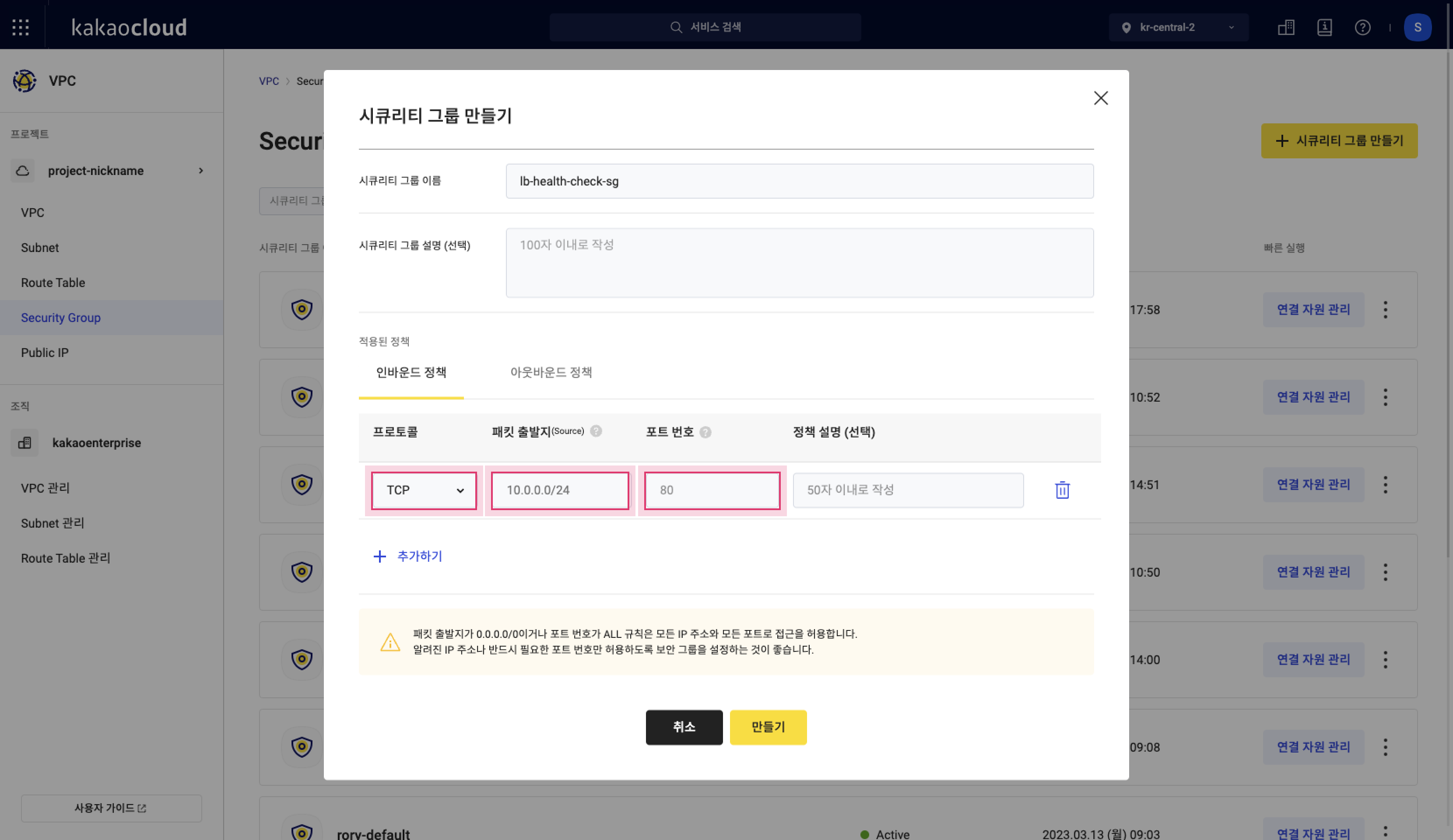 Create security group
Create security group -
Based on the detailed information in Step 3 of the Target group > Targets tab, enter all rule information.
- You can register all health check IPs in one security group and connect that security group to all target instances.
Or you can create a security group for each subnet, register only the health check IPs created in that subnet, and then connect it only to the target instances in the same subnet.
Category Description Protocol Protocol for communication (TCP, UDP, ICMP, ALL), selected according to the health check type of the target group
- If the health check type is PING:ICMP
- If the health check type is HTTP, HTTPS, TCP:TCPSource Source IP to allow access
- Enter the health check IP confirmed in target details
- Register each of the two health check IPs created in the subnet that contains the target
- If managing with one security group, register each of all health check IPsPort Port for communication
- Enter the health check port of the target
- Can be entered as a single port or a rangeRule description (optional) Description of the rule - You can register all health check IPs in one security group and connect that security group to all target instances.
-
Click the [Create] button to complete security group creation.
-
In the Security group list, click the [Manage connected resources] button on the right of the created security group to connect the target instance and complete the configuration.
Set health check port
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Select the target group for which you want to change health check port settings.
- Click the Targets tab, and then click [⋮] > Set health check port.
- Change the health check port value in the pop-up window to suit your environment, and then click the [Save] button.
View target list and basic information
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Click the target group for which you want to view targets.
- On the details page, select the Targets tab.
- Check the target list and basic information of the targets.
Category Description IP Target IP Port Target port Instance Name and ID of the target instance Subnet Name of the subnet that contains the target Security group Security group connected to the target instance Health check port Port on which the health check is performed Weight ratio Weight ratio converted from the entered weight according to the formula Provisioning status Indicates whether the target was added successfully or whether modification or deletion is in progress Operating status Indicates whether the added target is available for use [⋮] button Provides Set health check port and Disassociate target functions
Modify targets
You cannot modify the port of an added target. If you want to change the port, delete the target and then add it again by using Configure targets.
Detach target
- Go to KakaoCloud console > Networking > Load Balancing > Target group.
- Select the target group from which you want to disassociate a target.
- Select the Targets tab, and then select [⋮] > Disassociate target for the target.
- Enter the information in the pop-up window, and then click the [Detach] button.
Disassociating a target does not delete the instance. To associate it again, add it in Configure targets.